The 'Dark Net' Holds Internet's Secrets
DENVER (CBS4) - A day after the U.S. Department of Justice announced the largest theft of consumer financial data in U.S. history, a CBS4 investigation shows where financial and personal information is routinely bought and sold.
Cyber thieves aren't selling hacked information on street corners, they're doing it in the shadows of the Dark Net.
Twice in the last month, Denise Hoffman has been notified her accounts have been hacked; first from a health care company, then from her cellphone provider.
"It's a really big violation," she said. "It's a scary moment when you have a lot of exposure and things can be taken from you."
One notification stated the hackers may now have her Social Security number, financial information and even her medical history.
"It's just ridiculous. It's everything. I can't think of more things I can add to it," Hoffman said.
She figures it's just a matter of time before someone tries to use her identity.
"I'm worried about the long-term effect. Once they have it, it doesn't go away," she said.
The malicious results of a hack won't always show up immediately because information is often bought and sold multiple times on the 'Dark Net,' a hidden part of the Internet most people never see.
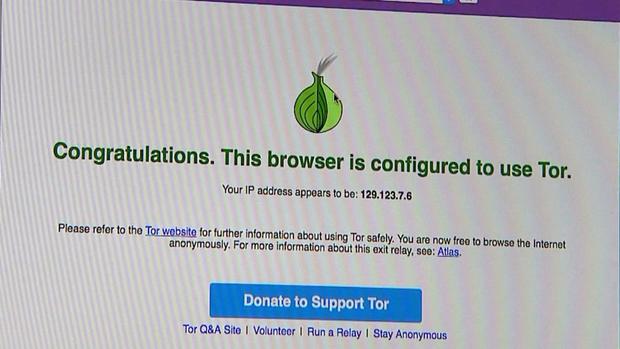
Metro State University Computer Science Professor Steve Beaty explains people can only access the Dark Net with a special browser called The Onion Router, or TOR, which anonymizes every interaction.
Once you get to the Dark Net, it is easy to find all kinds of criminal activity.
Beaty showed CBS4 a Dark Net search engine that is designed to look like Google. He then went to .onion websites (as opposed to .com, .net, or .org), where you can order a phishing attack, buy a bank account or a batch of credit cards.
If you have enough bitcoin, the encrypted currency of the Dark Net, you can buy a specific person's most personal information including Social Security number, date of birth and financial information.
"If you get the 'fullz' you can impersonate a person," said Beaty.
The Dark Net is also a wide open marketplace for illegal guns, drugs, passports and even hitmen.
"That's very concerning," said Beaty. "We are talking about contract murder and burning down buildings."
But there are also people like Dale Drew, trying to stay one step ahead of the hackers.
"This is our threat map of actual attacks that are happening on the nternet right now," said Drew, the Chief Security Officer at Level 3 Communications, who monitors hacks in real time and tries to prevent them.
To protect yourself from a data breach, Drew recommends choosing a complex password and changing it frequently. Also, reboot your computer frequently and deploy software updates when they come out.
Drew stores his personal data on an encrypted USB drive that he takes home at night. If that fails he backs up his information on a coin with a hidden chip stored inside.
Drew says the only way to bat the hackers and keep your personal information off the Dark Net is to stay vigilant.
"The bad guys do not take vacations," he said.
The Onion Router was originally created by the U.S. Naval Laboratories in the mid-1990s with the purpose of protecting U.S. intelligence communications online. The anonymity that allows criminal activity to thrive provides a platform for whistleblowers and freedom of speech.
Additional Resources
The Tor network is a group of volunteer-operated servers that allows people to improve their privacy and security on the Internet.
Mark Ackerman is a Special Projects Producer at CBS4. Follow him on Twitter @ackermanmark